Top Data Protector Free Download 2025 For Windows 11/10
Top Data Protector Free Download 2025 For Windows 11/10
Safeguarding Your Digital World
in today’s digital age, where our lives are intricately woven into the fabric of technology, safeguarding our data has become more critical than ever before. Whether it’s personal photos, financial records, or sensitive business information, the need for a reliable and efficient data protector has never been greater.
This is where the Top Data Protector comes into play, offering a free download solution that promises to keep your digital world secure. In this comprehensive guide, we will explore what makes a standout choice for data security, how to download and install it, and some of its key features.
Why Do You Need a Data Protector?
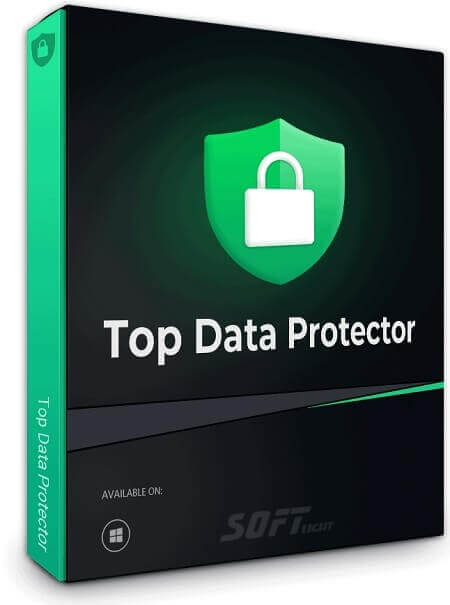
Before we delve into the specifics of the Top Data Protector, let’s address the fundamental question: Why do you need a data protector? In today’s interconnected world, data is a valuable commodity. Whether you’re an individual or a business, your data is constantly at risk from various threats such as cyberattacks, malware, or accidental deletions. Here are some reasons why having a robust data protector is essential:
- Data Security: Protecting your data ensures that it remains confidential and is not accessible to unauthorized individuals or cybercriminals.
- Data Recovery: In the event of data loss due to hardware failure or accidental deletion, a data protector can help you recover your valuable information.
- Preventing Data Theft: Cyberattacks are on the rise, and a data protector acts as a barrier against hackers attempting to steal your sensitive information.
- Maintaining Business Continuity: For businesses, data protection is crucial for maintaining operations and preventing downtime.
Introducing
Now that we understand the importance of data protection, let’s dive into what makes them stand out from the crowd.
Free Download and Easy Installation
One of the most attractive aspects is that it offers a free download. This means you can get started on securing your data without any initial cost. The installation process is user-friendly, making it accessible even for those who may not be tech-savvy.
Comprehensive Data Encryption
Employs state-of-the-art encryption techniques to ensure that your data remains impenetrable to unauthorized access. It uses advanced algorithms to encrypt your files, making them virtually impossible for anyone to decipher without the proper encryption key.
Regular Data Backups
To add an extra layer of security, it provides an option for automated data backups. This feature ensures that even in the worst-case scenario, where data is lost or compromised, you can easily restore it from a previous backup.
Real-time Threat Detection
Cyber threats are evolving constantly and it stays ahead of the curve with its real-time threat detection capabilities. It actively monitors your system for any suspicious activities or potential threats, alerting you promptly so you can take action.
User-Friendly Interface
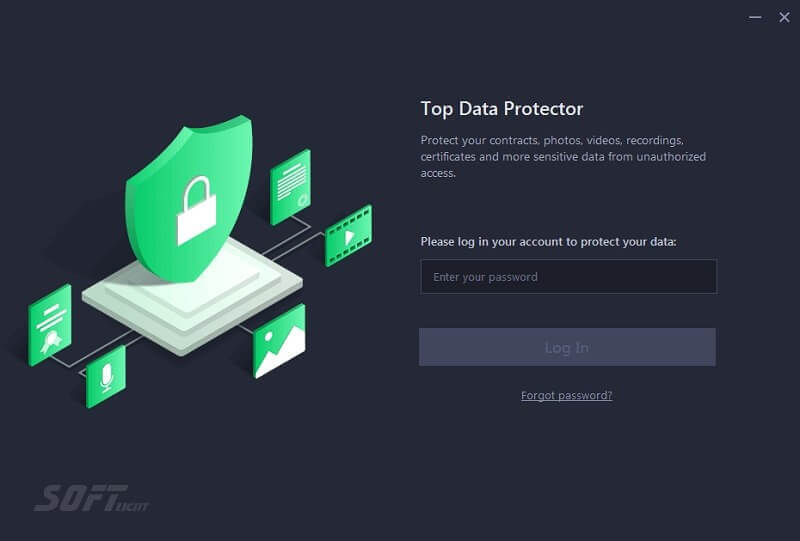
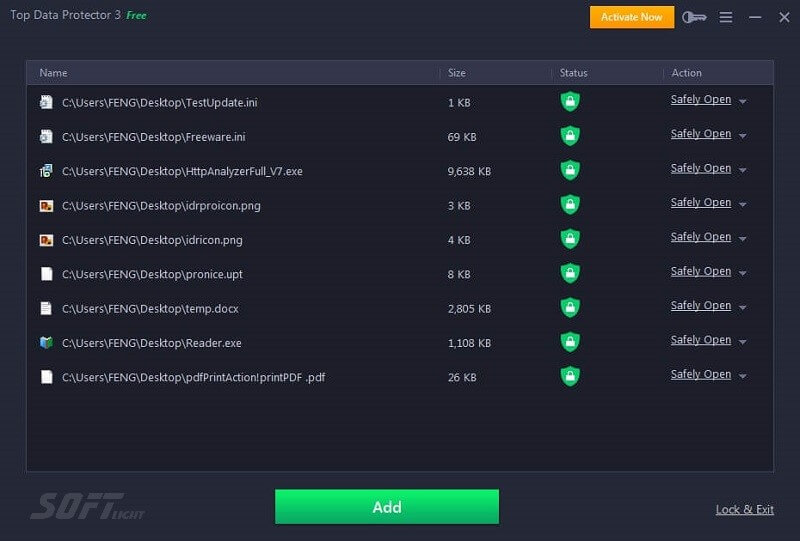
Navigating through it is a breeze, thanks to its intuitive user interface. Whether you’re a beginner or an experienced user, you’ll find it easy to access and customize the settings according to your preferences.
How to Download and Install
Now that you’re eager to try out the Top Data Protector, let’s walk through the simple steps to download and install it on your device.
- Visit the official Website: Start by visiting the official website. You can easily find it through a quick internet search.
- Download the Software: On the website, you’ll find a prominent “Download Now” button. Click on it to initiate the download.
- Run the Installer: Once the download is complete, run the installer file. Follow the on-screen instructions to complete the installation process.
- Launch the Application: After successful installation, launch the application. You may need to create an account or log in, depending on the software’s requirements.
- Customize Your Settings: Explore the software’s settings to configure it according to your data protection needs. You can set up automated backups, adjust encryption settings, and enable real-time threat detection.
- Start Protecting Your Data: With the Top Data Protector installed and configured, you’re now ready to start safeguarding your digital world. The software will work silently in the background, ensuring your data remains secure.
Why System Requirements Matter
Before we delve into the specifics of system requirements, let’s discuss why they are crucial. System requirements provide essential information about the hardware and software configurations needed to run a particular application effectively. Ignoring these requirements can result in a subpar user experience, system crashes, or even complete incompatibility.
When it comes to data protectors, knowing the system requirements is vital because these tools often operate at a deep level within your system. If your system doesn’t meet these requirements, you might compromise the security and functionality of your data protection software. Now, let’s explore the system requirements available for free download.
System Requirements
Operating System Compatibility
One of the fundamental aspects of system requirements is the compatibility with different operating systems. The top data protector we’re discussing here offers versatile compatibility, making it accessible to a wide range of users. You can download and install it on the following operating systems:
Windows:
- Windows 11/10
Hardware Requirements
Apart from operating system compatibility, you need to ensure your hardware meets the data protector’s requirements. Here are the hardware specifications you should consider:
- Processor: A modern multi-core processor (64-bit) is recommended for optimal performance.
- RAM: A minimum of 2GB RAM is required, but 4GB or more is recommended for smoother operation.
- Disk Space: The software installation typically requires around 1GB of free disk space, but the amount of space needed for backups depends on your data volume.
Additional Software and Connectivity
To fully utilize the features, you’ll also need:
- Internet Connection: An internet connection is required for downloading and updating the software and for remote backup options.
- Browser: For the web-based management console, a compatible web browser (e.g., Chrome, Firefox, or Edge) is necessary.
Pros of Top Data Protector
- Cost-Effective Solution: The most obvious advantage of opting for a free download option is cost savings. Users can secure their data without shelling out a dime, making it an attractive choice for individuals and small businesses with budget constraints.
- User-Friendly Interface: Many free offer intuitive and user-friendly interfaces, making them accessible even for those without advanced technical skills. This simplicity ensures that a broader range of users can benefit from data protection.
- Basic Data Security: Free typically provides fundamental data security features like file encryption, password protection, and data backup. These features are often sufficient for individuals and small businesses looking to protect their essential files.
- Trial Periods for Premium Features: Some free tools offer trial periods for their premium features. This allows users to experience the full range of protection options before deciding whether to upgrade to a paid version.
Cons
- Limited Features: While free offer basic security features, they often lack the advanced functionalities available in paid versions. These limitations may include fewer customization options, limited customer support, and reduced compatibility with diverse devices and operating systems.
- Ads and Pop-Ups: Free software often relies on advertising revenue to sustain itself. Consequently, users may encounter intrusive ads and pop-ups while using the tool. These distractions can be frustrating and hinder the user experience.
- Limited Customer Support: Free people typically provide limited customer support compared to their paid counterparts. Users may struggle to find assistance when facing issues or seeking guidance on complex configurations.
- Risk of Unreliable Software: Not all free data protectors are created equal. Some may be developed by less reputable companies, raising concerns about the reliability and security of the software itself. Users should exercise caution and choose a well-established, trusted tool.
Choosing the Right Data Protector for You
Ultimately, the decision to invest in a paid one depends on your specific needs and priorities. If you’re an individual or small business with basic data security requirements and a limited budget, a top data protector with a free download option may suffice. However, if you demand advanced features, reliable customer support, and a premium level of security, it’s advisable to explore paid options.
Conclusion
In an era where data is a currency and its protection is paramount, the Top Data Protector emerges as a reliable ally. With its free download option, robust encryption, real-time threat detection, and user-friendly interface, it offers a comprehensive solution to keep your digital world safe.
Don’t wait until a data disaster strikes; take proactive steps to protect your valuable information today. Download it and fortify your digital fortress against the ever-present threats of the cyber world. Your data deserves nothing less than the best.
📌 Remember, in the digital realm, it’s not a matter of if a threat will occur but when. Secure your data with the Top Data Protector—your shield against the unknown.
Download it today and enjoy peace of mind in the digital age. Your data security is just a click away!
Technical Details
- Category: System Security
Software name: Top Data Protector
- License: Demo
- File size: 9 MB
- Kernel: 32, 64 bits
- Operating systems: Windows XP, Vista, 7, 8, 8.1, 10, 11
- Languages: Multiangular
- Developer: iTop Inc
- Official site: itopvpn.com