Firewall App Blocker Free Download 2025 Essential Security
Firewall App Blocker Free Download 2025 Essential Security
Unleashing the Power of Firewall App Blocker: A Comprehensive Guide
In an era dominated by technological advancements, ensuring the security of our digital realm is of paramount importance. With the increasing threat landscape, the need for robust cybersecurity tools has never been more critical.
Enter and cutting-edge solution designed to fortify your digital defenses and empower you with unparalleled control over your applications.

Understanding the Essence
What Sets Apart?
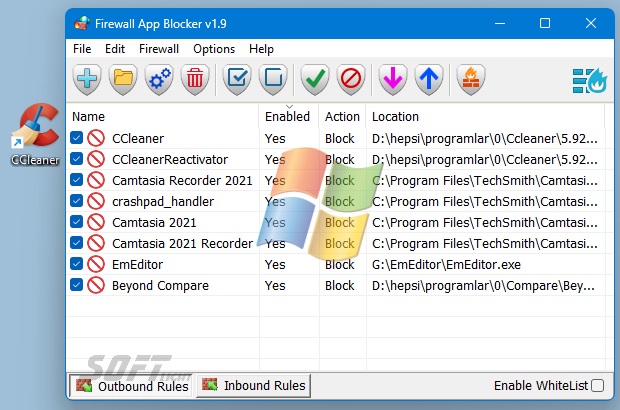
Firewall App Blocker stands out as a formidable guardian, providing an extra layer of protection against malicious entities attempting to infiltrate your system. Unlike conventional firewalls, this advanced tool goes beyond the basics, offering an array of features that redefine the standards of application security.
Unveiling the Features
- Application Whitelisting and Blacklisting: Take charge of your system by deciding which applications are permitted and which are denied access. It allows you to create customized lists, granting you control like never before.
- Real-time Monitoring and Alerts: Stay informed about your system’s activities with real-time monitoring. Receive instant alerts whenever suspicious activities or unauthorized access attempts are detected.
- User-Friendly Interface: Navigating through the complexities of cybersecurity has never been easier. The intuitive user interface ensures that both novices and tech-savvy individuals can harness its power effortlessly.
- Customizable Security Policies: Tailor the security protocols to align with your specific needs. Define rules and policies that suit your workflow, ensuring a seamless user experience without compromising on safety.
Harnessing the Power in Your Daily Life
Securing Your Personal Space
Are you concerned about the security of your personal computer or mobile device? It becomes your digital guardian, preventing unauthorized access and potential threats, and allowing you to browse, work, and play with confidence.
Safeguarding Business Networks
For businesses, the stakes are higher. Proves to be an invaluable asset in safeguarding sensitive data, thwarting cyberattacks, and maintaining the integrity of business operations. Its scalability ensures that it adapts seamlessly to the evolving needs of any enterprise.
Installation and Configuration Made Simple
Step-by-Step Setup Guide
- Download and Installation: Begin by downloading it from the official website. Follow the straightforward installation process to integrate this powerful tool into your system.
- Configuration Wizard: The configuration wizard simplifies the setup process, guiding you through the initial settings. Define your preferences, security levels, and application permissions with ease.
- Regular Updates: Ensure that you stay abreast of the latest security measures by allowing automatic updates. Evolves continuously to counter emerging threats effectively.
Pros of Firewall App Blocker
1. Enhanced Security Measures:
Serve as virtual gatekeepers, meticulously monitoring incoming and outgoing network traffic. This heightened level of scrutiny adds an extra layer of security, preventing unauthorized access and potential cyber threats.
2. Customizable Filtering:
One significant advantage lies in the ability to customize filtering rules. Users can define specific criteria to regulate which applications are allowed or denied access to the network. This flexibility ensures that the firewall aligns with the unique security needs of the user or organization.
3. Protection Against Malicious Attacks:
The primary function is to thwart malicious attacks, such as malware, ransomware, and other cyber threats. By actively monitoring and controlling network traffic, these applications act as a first line of defense against potential breaches.
4. Anomaly Detection and Alerts:
Firewall App Blocker often comes equipped with advanced features, including anomaly detection and real-time alerts. This proactive approach enables users to identify and respond swiftly to unusual or suspicious network activities, mitigating potential security risks.
5. Safe Browsing Experience:
Users can enjoy a safer online experience with the aid. By blocking access to potentially harmful websites and applications, these tools contribute to a more secure digital environment.
Cons
1. Overblocking and False Positives:
One significant drawback is the potential for overblocking legitimate applications and generating false positives. Overly strict filtering rules may inadvertently prevent access to essential services, leading to frustration and productivity issues.
2. Resource Intensiveness:
Be resource-intensive, especially on older or less powerful hardware. Continuous monitoring of network traffic and the application of complex filtering rules may result in a slowdown of overall system performance.
3. Complex Configuration:
Configuring and fine-tuning a Firewall App Blocker to suit specific needs can be a complex task. Non-technical users may find it challenging to navigate the intricate settings and may inadvertently misconfigure the firewall, compromising its effectiveness.
4. Limited Protection Against Advanced Threats:
While effective against many common threats, it may have limitations when it comes to sophisticated and targeted attacks. Advanced threats that exploit vulnerabilities in the system may bypass the firewall’s defenses.
5. Cost Considerations:
Implementing a robust solution may come with associated costs. The investment in premium firewall services or dedicated hardware can be a factor for individuals or smaller organizations with budget constraints.

Key Features
Firewall App Blocker boasts a plethora of features, including but not limited to:
1. Advanced Packet Filtering
The application employs sophisticated packet filtering techniques to scrutinize data packets entering or leaving your network. This meticulous inspection allows people to permit or block data packets based on predefined rules, contributing to a robust defense mechanism.
2. Application-Level Filtering
Unlike traditional firewalls, it goes a step further by offering application-level filtering. This means it can control access to specific applications, adding an extra layer of security to your system.
3. Real-time Monitoring
The real-time monitoring capabilities empower users with instant insights into network activities. Any suspicious or unauthorized attempts are promptly identified, giving you the ability to take immediate action.
System Requirements
To harness the full potential, your system must meet certain prerequisites. Let’s delve into the specifics of the System Requirements:
1. Operating System Compatibility
It is designed to seamlessly integrate with a variety of operating systems. It is compatible with:
- Windows 10/11
- Windows 8/8.1
- Windows 7
Ensure your system is running one of these versions to guarantee smooth installation and operation.
2. Processor
The performance relies heavily on the processing power of your system. For optimal results, it is recommended to have a multicore processor with a clock speed of at least 2.0 GHz. This ensures that the application can handle the demands of real-time packet inspection and filtering efficiently.
3. RAM (Random Access Memory)
To facilitate seamless execution, your system should have a minimum of 4 GB of RAM. This enables the application to handle concurrent network activities and maintain optimal performance.
4. Storage
While the application itself doesn’t consume substantial disk space, it is advisable to have at least 20 GB of free storage to accommodate logs and other data generated during its operation.
5. Network Interface
Requires a standard network interface card (NIC) for effective communication with the network. Ensure that your system is equipped with a compatible NIC to avoid any connectivity issues.
Installation Guidelines
Now that we have outlined the System Requirements, let’s explore the step-by-step installation process:
- Download the Installer: Visit the official website and download the latest version installer.
- Run the Installer: Execute the installer file and follow the on-screen instructions to initiate the installation process.
- Configuration Settings: During installation, you will be prompted to configure settings such as network preferences and application-level rules. Customize these settings according to your security requirements.
- Completion: Once the installation is complete, it will be active and ready to safeguard your system.
Frequently Asked Questions (FAQs)
1. Is it compatible with all operating systems?
Firewall App Blocker is designed to be compatible with a wide range of operating systems, including Windows, macOS, and Linux.
2. How does the real-time monitoring feature enhance security?
The real-time monitoring feature constantly scans your system for unusual activities. Any suspicious behavior triggers instant alerts, allowing you to take immediate action and fortify your defenses.
3. Can I customize the security policies based on my specific needs?
Absolutely! Firewall App Blocker prides itself on its flexibility. Users can customize security policies, define application permissions, and create personalized blacklists and whitelists to meet their unique requirements.
Conclusion: Elevate Your Security
As we navigate the intricate web of the digital world, having a robust cybersecurity solution is non-negotiable. Emerges as a beacon of security, providing a comprehensive defense mechanism against ever-evolving cyber threats. Embrace the power of control, fortify your digital fortress, and experience a new era of cybersecurity”.
Product Details
- Category: System Security
Software name: Firewall App Blocker
- Version: Latest
- License: Free
- File Size: 1.22 MB
- Support systems: Windows Vista + SP1 / 7 / 8 / 10 /11
- Languages: English and supported by many other languages
- Developed company: Sordum Team
- Official Website: sordum.org